Trezor Wallet Review | The Ultimate Guide to Get You Started
If you have started your adventurous journey with cryptocurrency or are already experienced, finding a secure crypto wallet that supports your needs can be a daunting experience.
Luckily, today’s article will showcase an extensive Trezor Wallet review, so you can choose what is best for your crypto needs.
Why are Crypto Wallets Important?
For those who have just started their first crypto journey, understanding the concept of a crypto wallet, the types, and how Trezor can help you is mandatory as it can alleviate the situation.
Cold wallets are unlike regular wallets, and contrary to widespread belief, they do not physically hold cryptocurrencies. Instead, they store your public and private keys and provide digital signatures that authorize each transaction.
Types of Crypto Wallets
There are 3 main types of cryptocurrency wallets, and each one comes with some specific features.
Paper wallets
In a paper wallet, the keys are written on physical paper and stored somewhere, but there are better options than this, making using your crypto difficult.
Online wallets
When it comes to software wallets, the keys are stored online in an app or software, but we all know that this comes with many vulnerabilities that can quickly transform into financial theft, coin fraud, and permanent loss of crypto assets.
Hardware wallets
In this case, the keys are stored on a thumb-drive device and only connect to a computer when accessing your cryptocurrencies.
The basic idea is that each one of them has its trade-offs, but as Trezor is the oldest hardware wallet around, still to this day, it remains one of the best in both reputation and affordability.
Trezor Wallet Review: Overview
Trezor is the very first crypto hardware wallet that was ever created. The wallet was launched in 2014 by Satoshi Labs, a Czech-based firm that has produced many innovations in terms of crypto products.
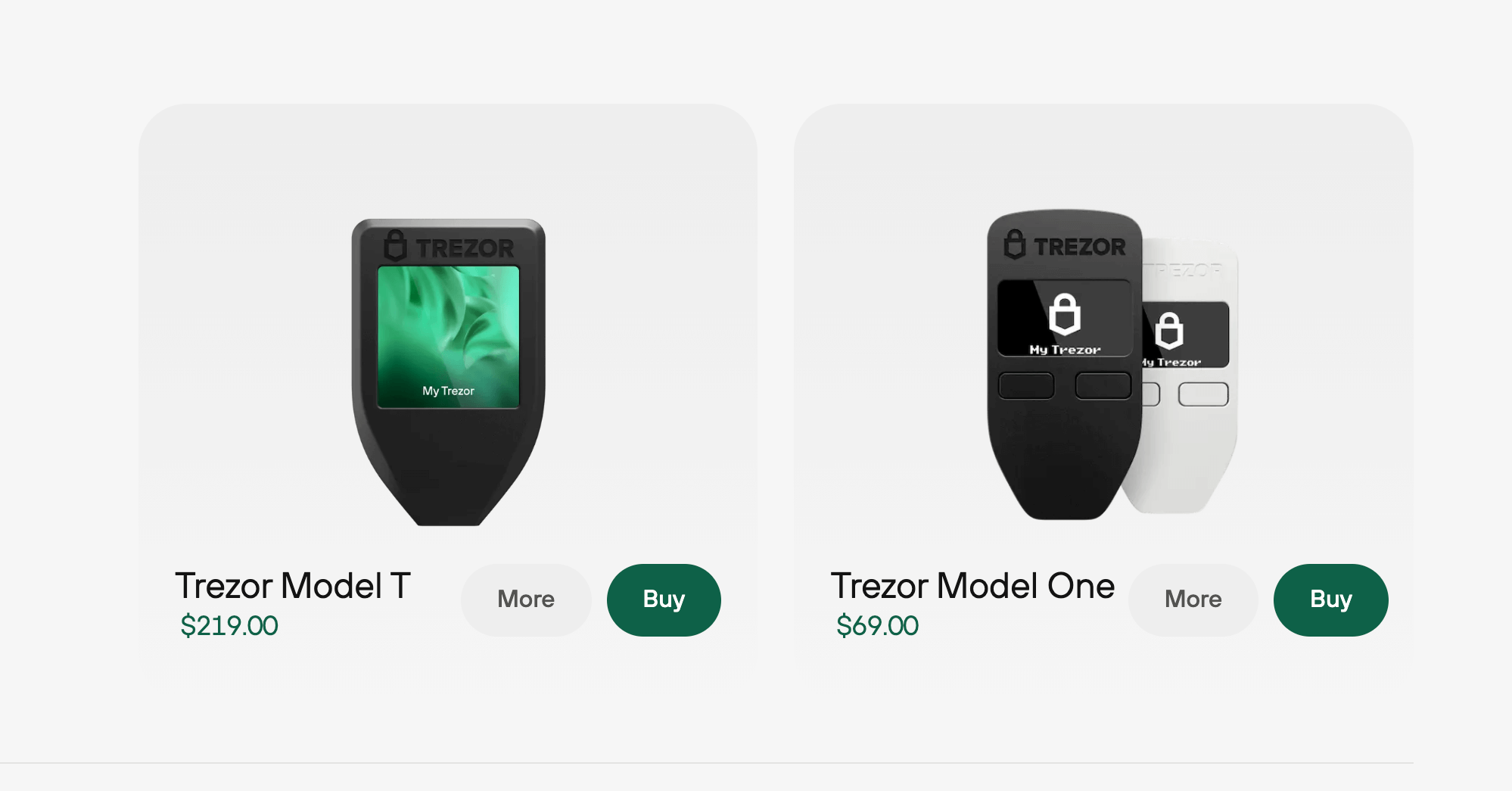
The company’s two wallet models, Trezor One and Trezor Model T, are compact hardware wallets that support various crypto, keeping them safe offline.
Other Cold Wallets
Another brand in the hardware wallet realm is Ledger, and the main two differentiators are that Ledger supports over 5,000 currencies instead of 1,816 on Trezor.
Second, Ledger has a mobile app for iOS and Android, and Trezor doesn’t, but isn’t this mobile app something that could jeopardize the safety of your holdings?
ELLIPAL Titan could be another hardware wallet option. It manages NFTs and supports over 10,000 coins & tokens, but it can be too pricey. However, using the QR codes instead, Ellipal eliminates the USB or Bluetooth connections.
Trezor Models Review: Design and Hardware
The interface has been updated several times to make the wallet user-friendly. Trezor Model T has a touchscreen feature, allowing users to easily find and manage their cryptos, compared to the Model One, which has a 1.54″ Color LCD touchscreen.
Its exterior has a small and compact design, with Trezor being around the size of a car key, which you connect to your PC via a USB C cable.
Regarding security, Trezor One can be accessed via computer instead of a PIN & passphrase entry featured in Model T.
Trezor Wallet Review: Set-up Your Trezor One
If you wonder where to buy a Trezor wallet, as mentioned, you can purchase your device directly from the manufacturer or official resellers to avoid risks.
To start the setup, you will need the Trezor Model One, a USB connecting cable, the Trezor Suite desktop app (alternatively, you can use Trezor Suite for the web), and a recovery seed card. For this, we are going to use the Trezor Suite desktop.
1. Trezor Suite desktop app will prompt you to connect your device;
2. You will have to do a quick security check – when unboxing the Trezon One, please ensure that your packaging is intact and the seal is not tempered, otherwise contact the customer support department;
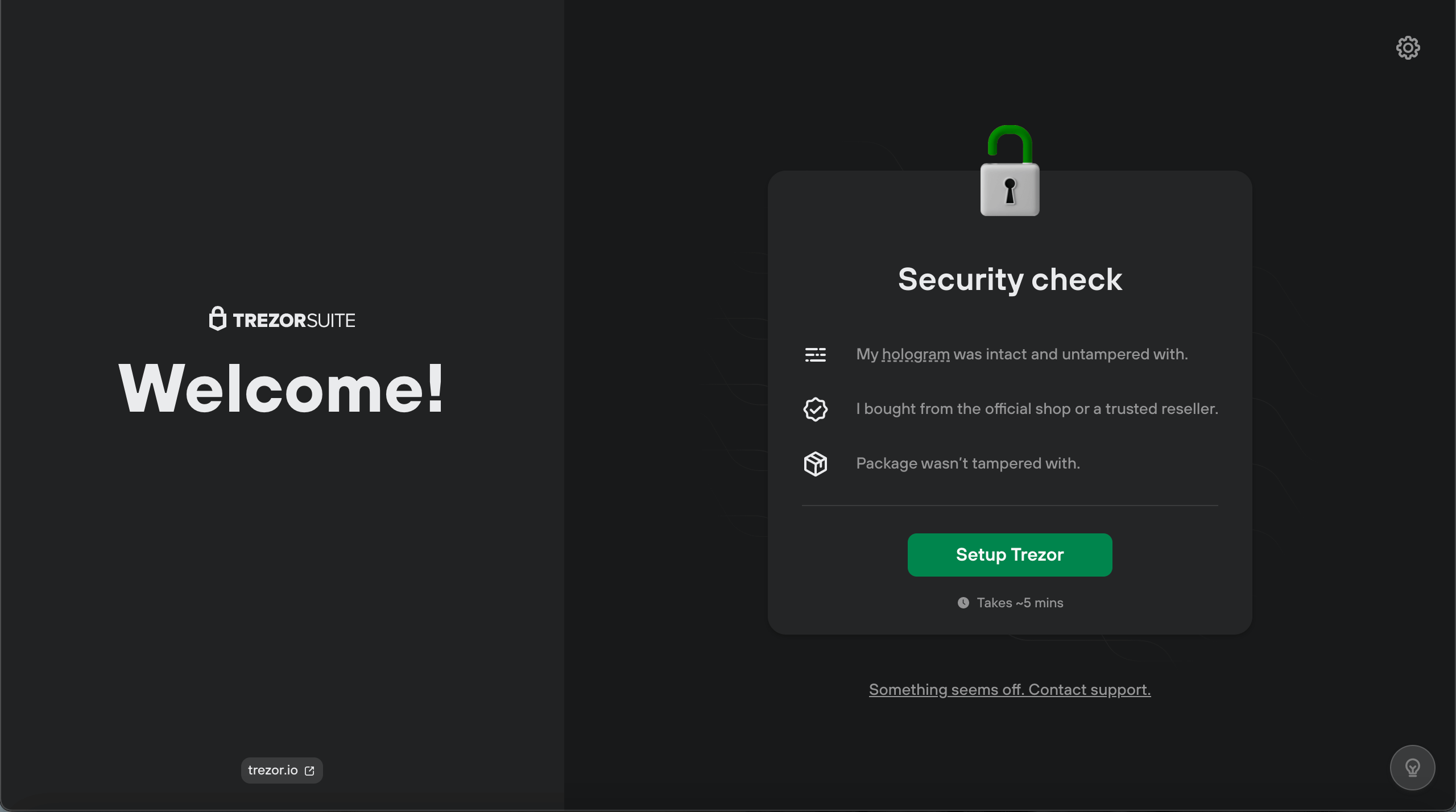
3. Once everything is correct, click ‘Setup Trezor’;
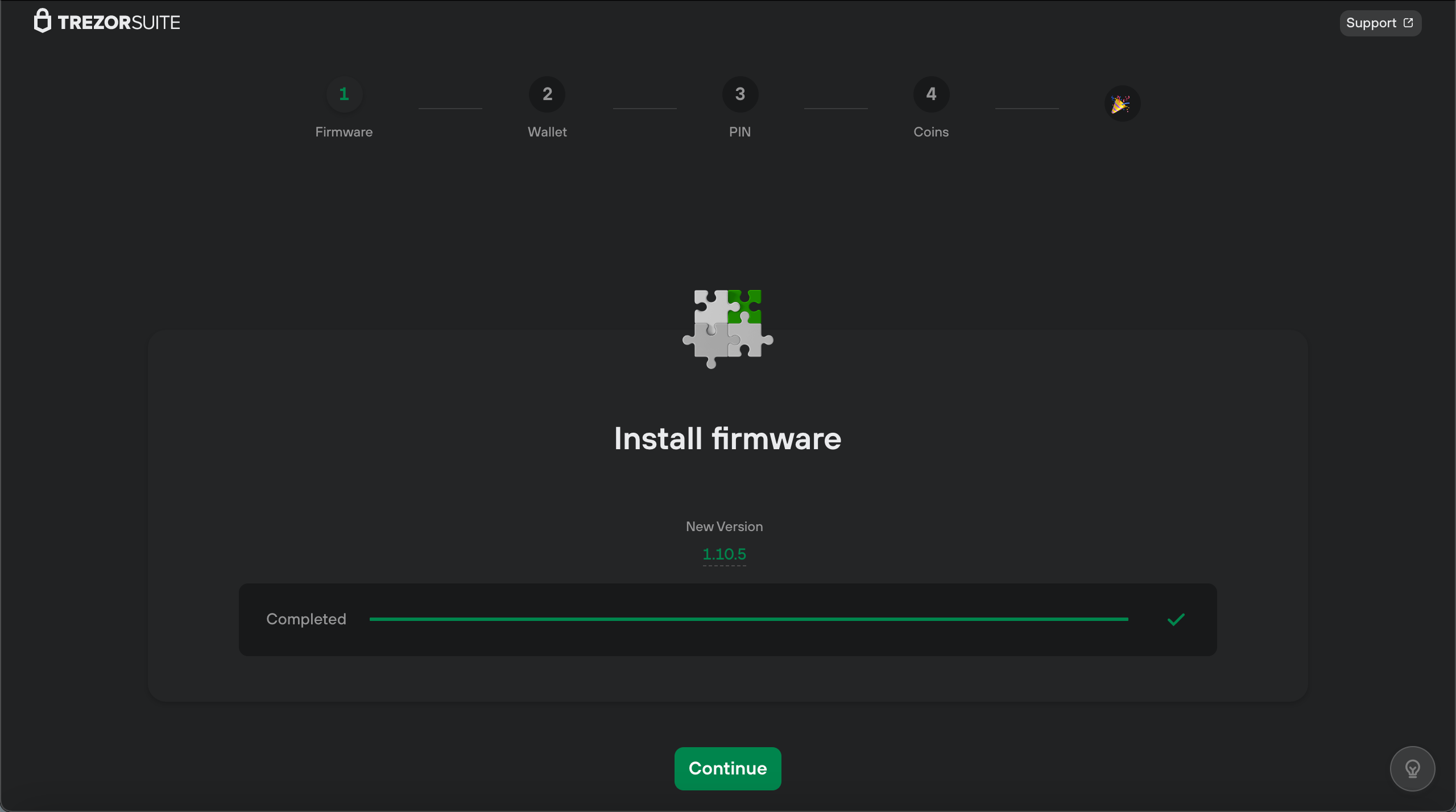
4. Click ‘Install firmware,’ as your Trezor One is shipped without, and you’ll need the latest version;
5. Once the installation is completed, click on ‘Continue’;
6. Click on ‘Create new wallet’ or use the ‘Recover wallet’ option if you already have a recovery seed backup;
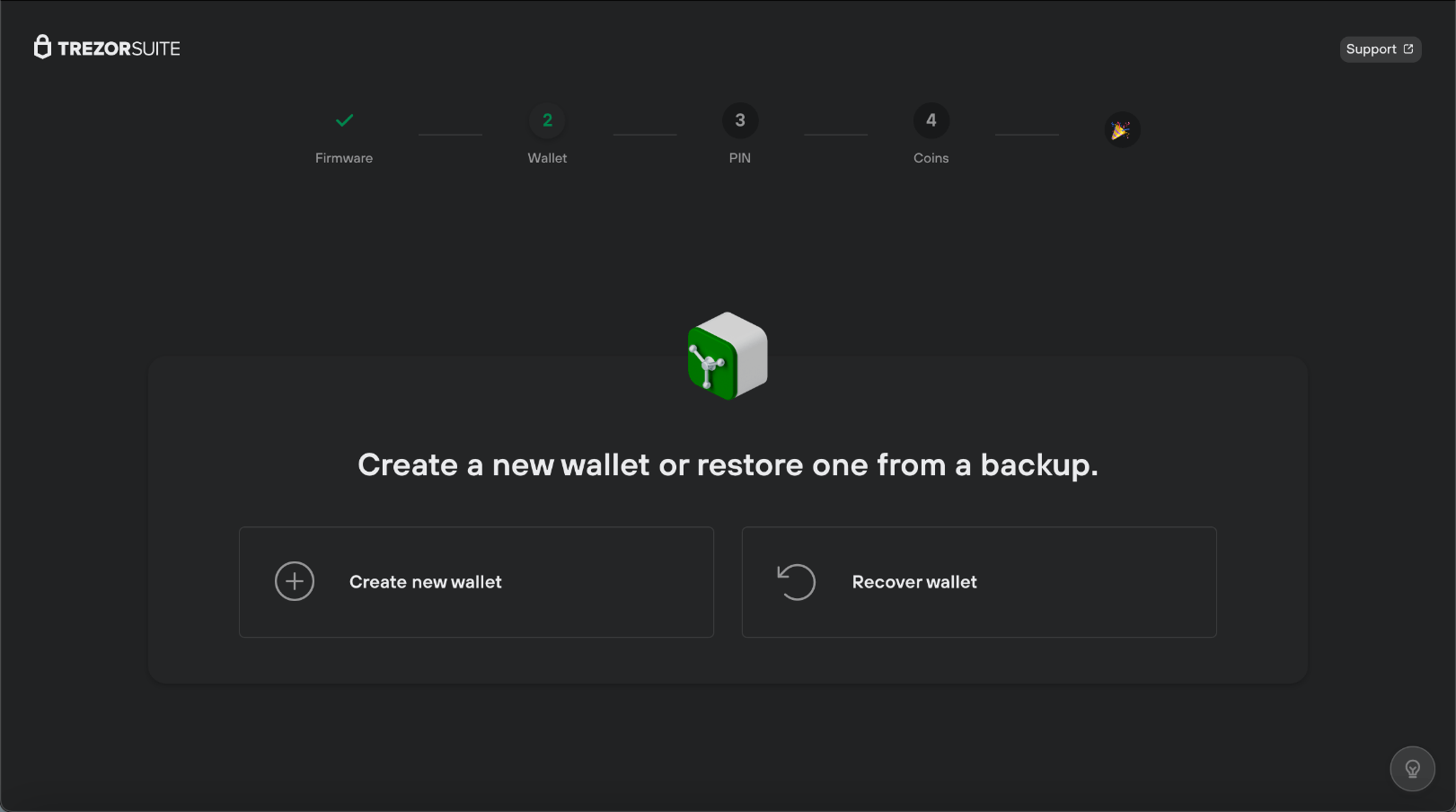
For this Trezor review, we will select the option to create a new wallet. Afterward, you will be prompted to choose ‘Standard seed backup’ to set up your recovery phrase;
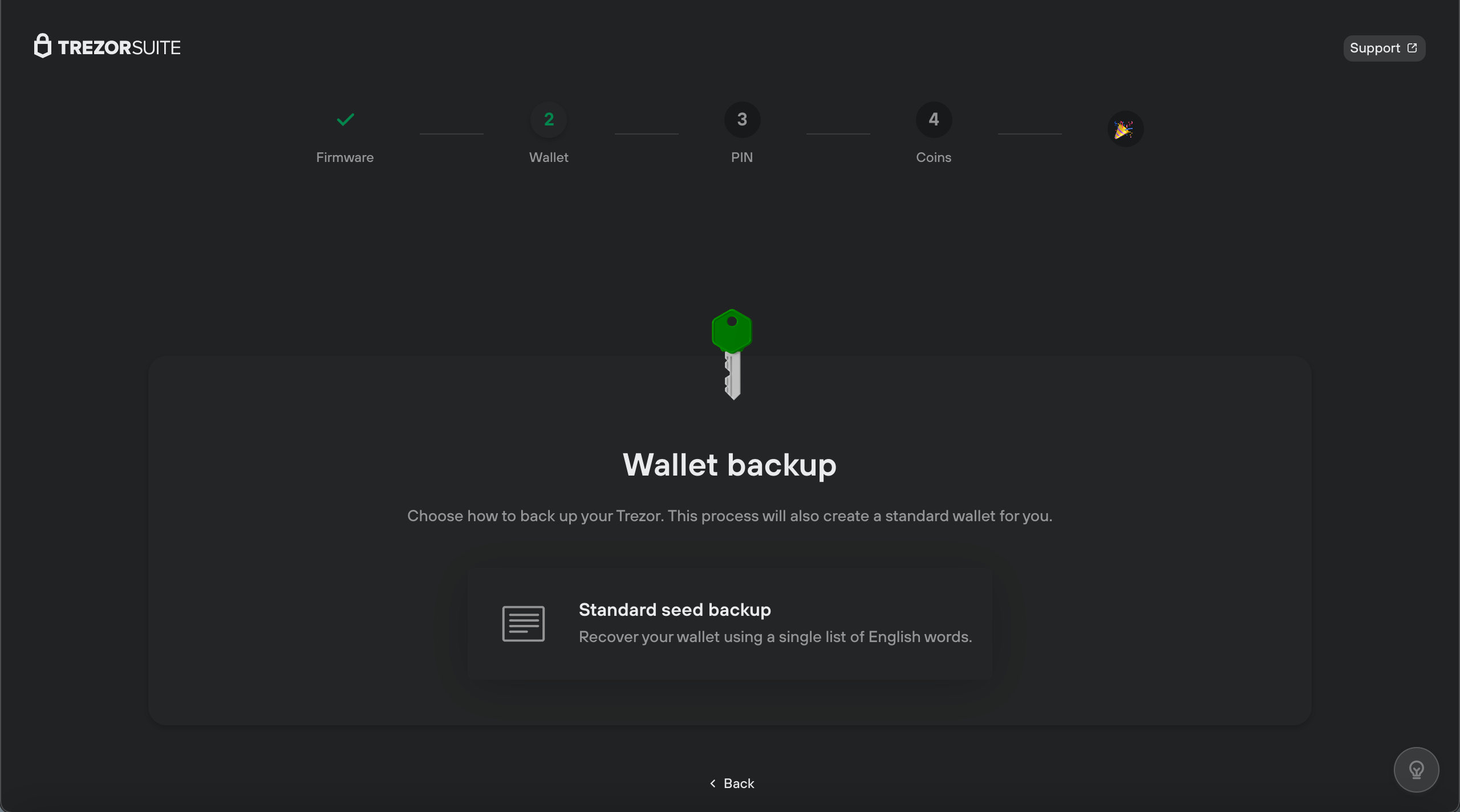
7. Press the ‘Confirm’ button on your device;
8. The following mandatory step is creating the backup and recording your recovery seed phrase on the recovery seed card provided. To begin the process, simply click ‘Create backup;’
9. Once you have all the green check marks, you can hit ‘Begin backup’;
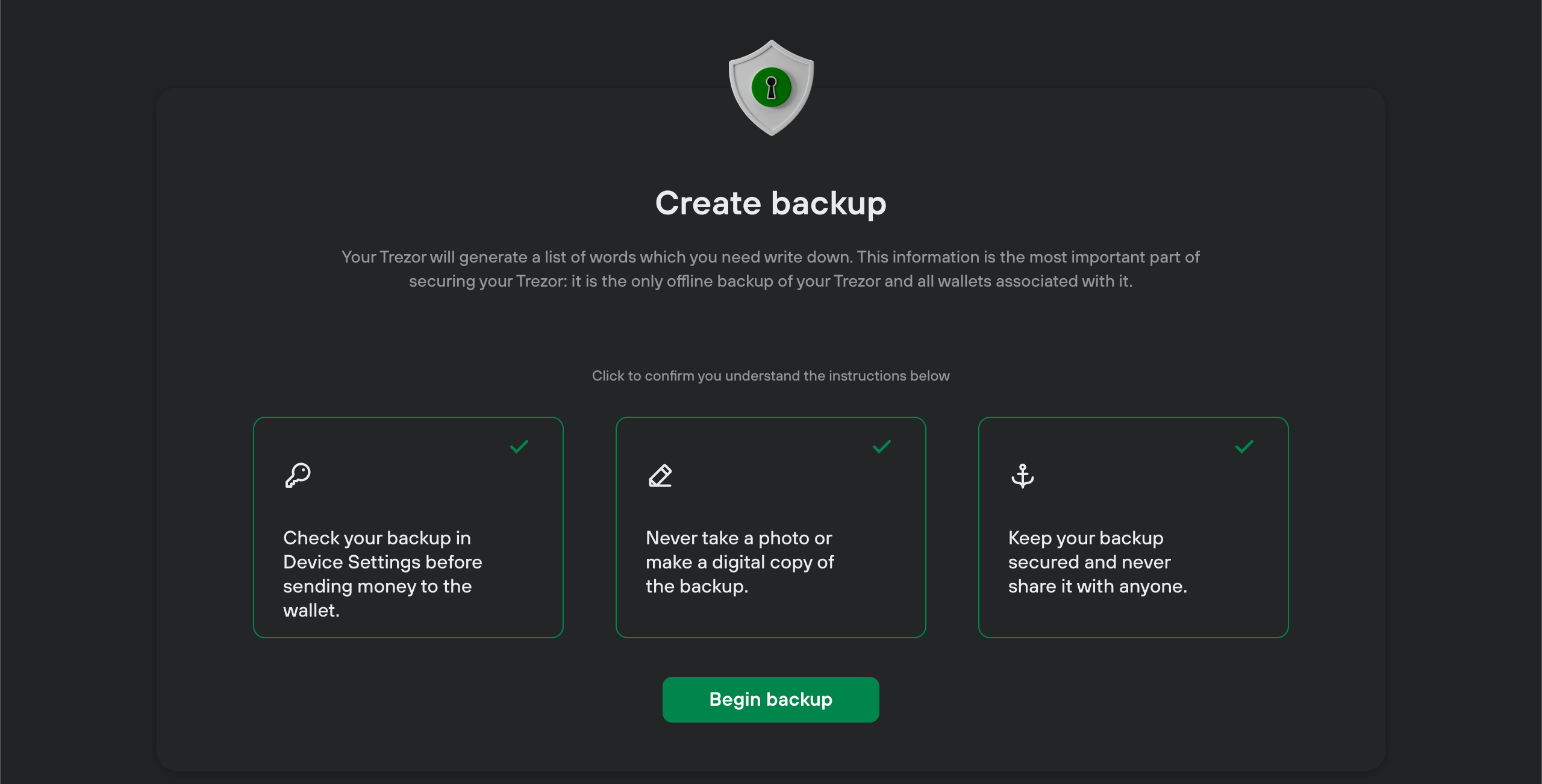
10. After pressing your device’s ‘Confirm’ button, your Trezor will generate a list of words. Write down the words correctly, pressing the button on the device to move to the next ones. You can write your 24 words on the provided recovery cards;
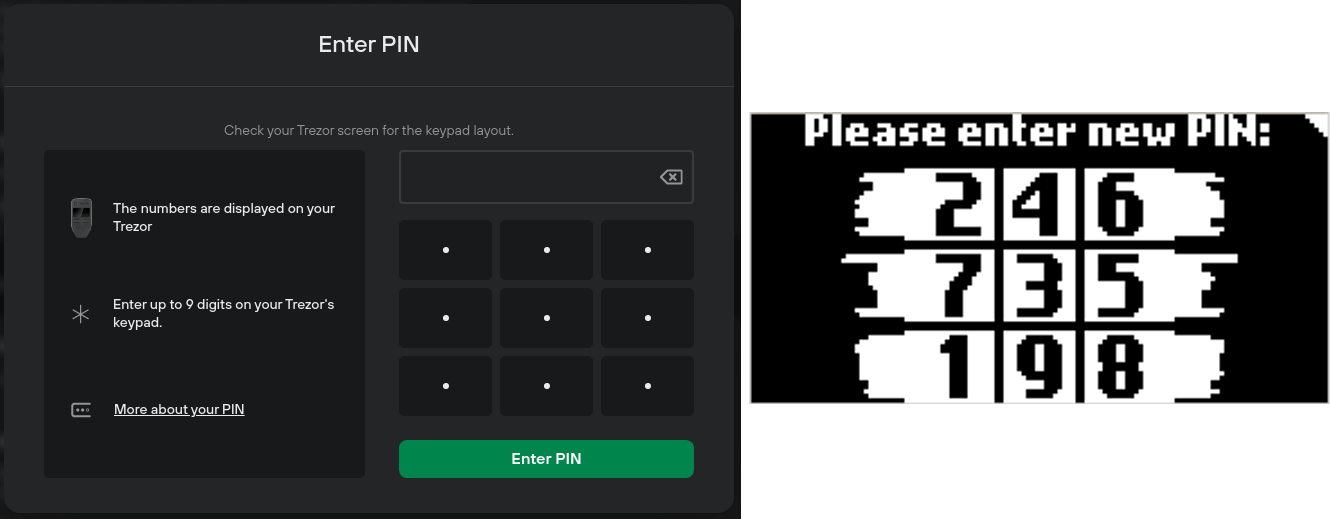
11. Once you have finished recording your words in the correct order, it is time to start setting up the PIN to protect your device. Click ‘Continue to PIN’;
12. At this point, you’ll be able to see the ‘Set a PIN’ page;
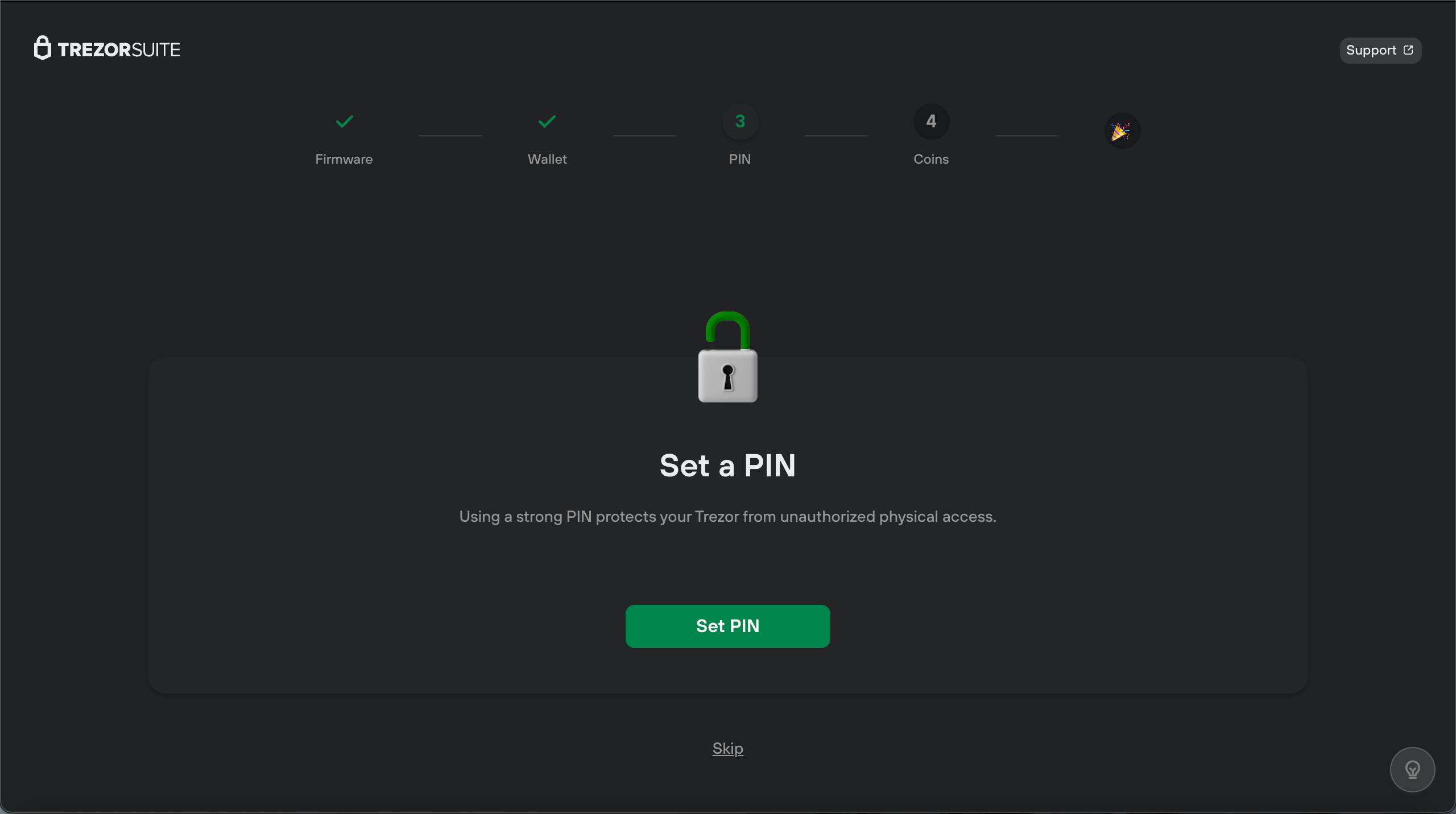
13. Once the PIN setup is done, you will be redirected to activate the coins window, where you can choose from the cryptocurrencies shown in Trezor Suite.
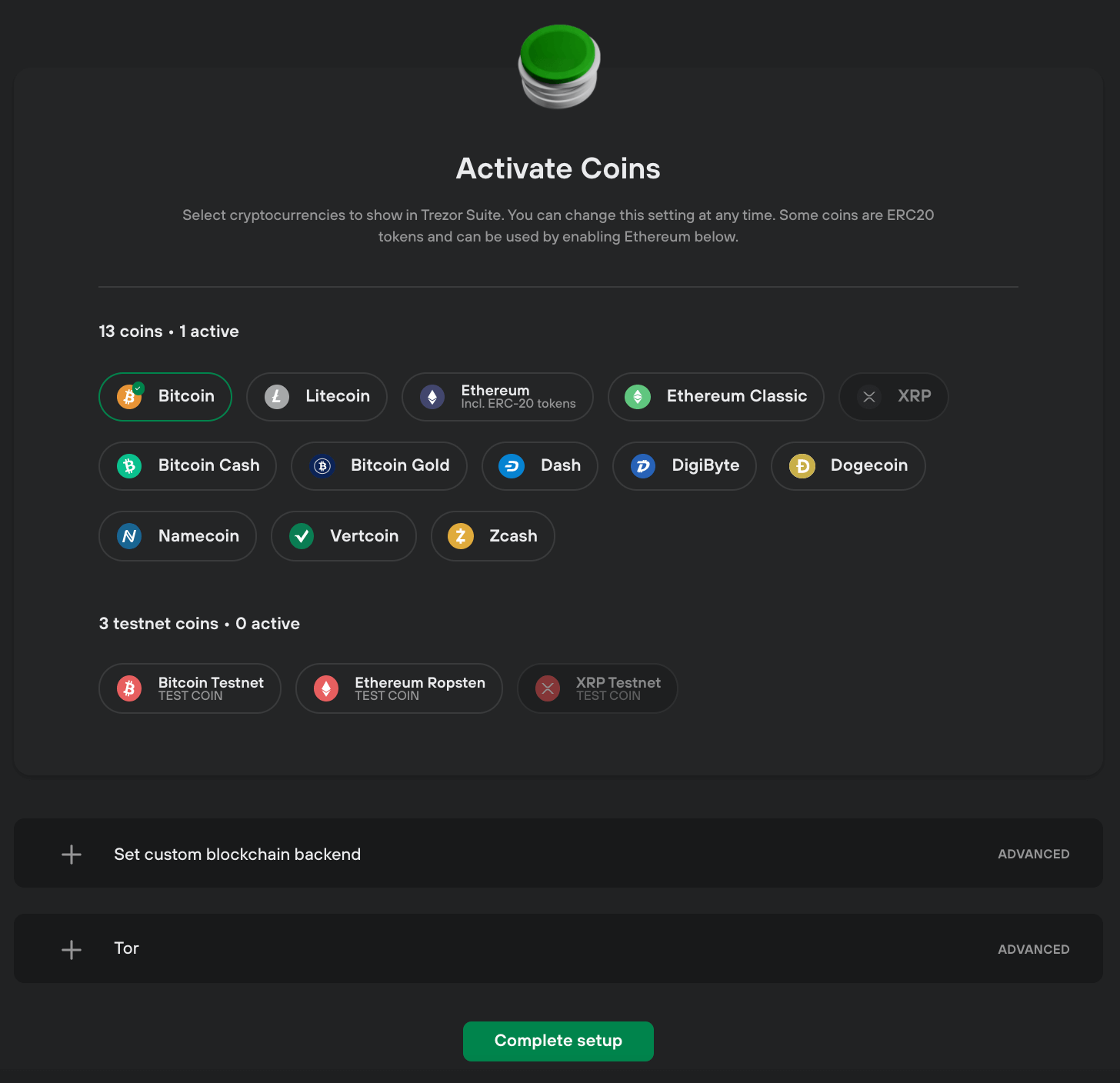
14. Once you are happy with your selection of active coins, click ‘Complete setup,’ and you are all done!
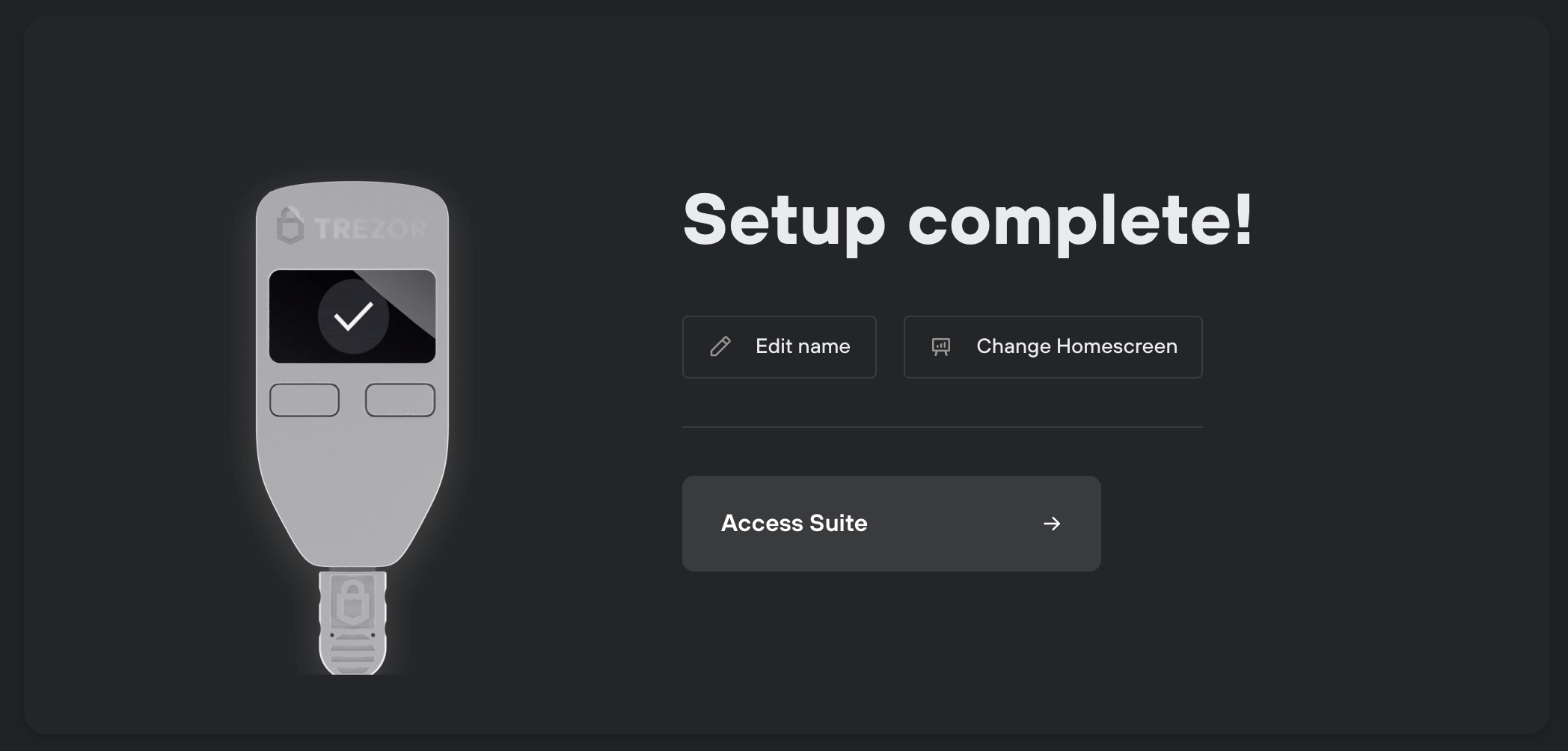
At this point, you can name your Trezor One, and access the Suite, to choose which type of wallet you want. You can either select ‘Standard wallet’ or ‘Hidden wallet.’ For the hidden wallet, a passphrase is required. Once you finish this, your wallet is ready for use.
How to Use Trezor Wallet
Adding Cryptocurrencies to Trezor Wallet
The Suite app or website has a user-friendly design and offers straightforward processes. For this Trezor review, we will show how to add cryptos to your Trezor wallet.
Trezor Suite supports Bitcoin, Litecoin, Ethereum, Ethereum Classic, Ripple, Dash, Zcash, DigiByte, Namecoin, Dogecoin, Vertcoin, Bitcoin Cash, Bitcoin Gold, and Cardano. ERC20 tokens can be received using an Ethereum account.
So, without further ado, let’s get started.
- Under the ‘My accounts’ sidebar menu, you can see your supported cryptocurrency accounts. Choose which crypto to add to your wallet and click the ‘Receive’ tab.
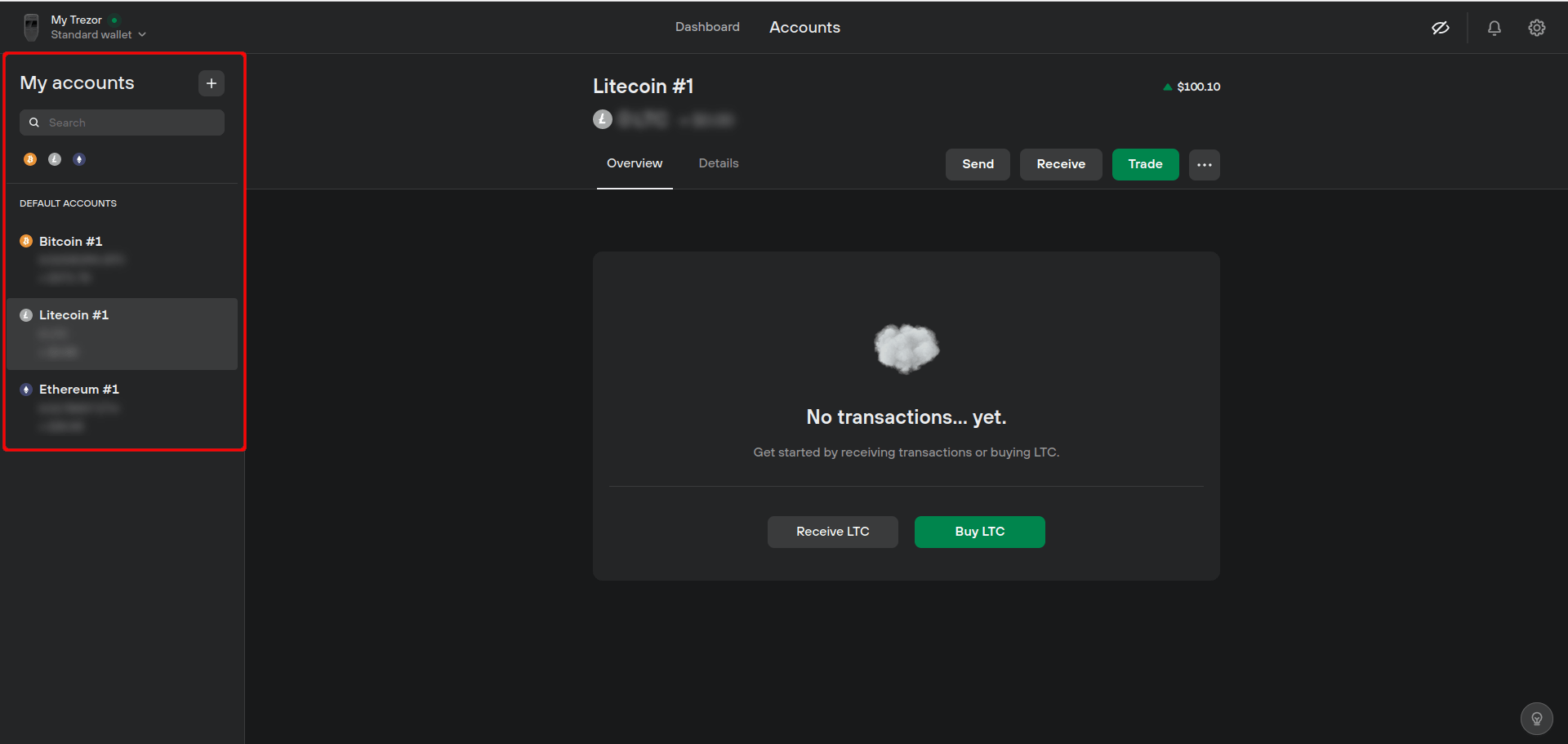
- Click ‘Show full address’ to view your device’s wallet address. At this point, you will be asked to confirm this address on your Trezor. Compare the address shown in the Suite with the one on your Trezor One.
- Copy this address to send your funds from another wallet or exchange account.
Making Payments on Trezor Wallet
Once you have plugged in your Trezor One device, go to the ‘Accounts’ page in your Trezor Suite.
- Select the one you want to send and send funds between accounts of the same cryptocurrency. Otherwise, mixing cryptocurrencies is likely to end in a loss of funds;
- Click on the “Send” tab;

- Enter the destination address and how much you want to send. Just so you know, there are four types of priority, thus transaction fees.
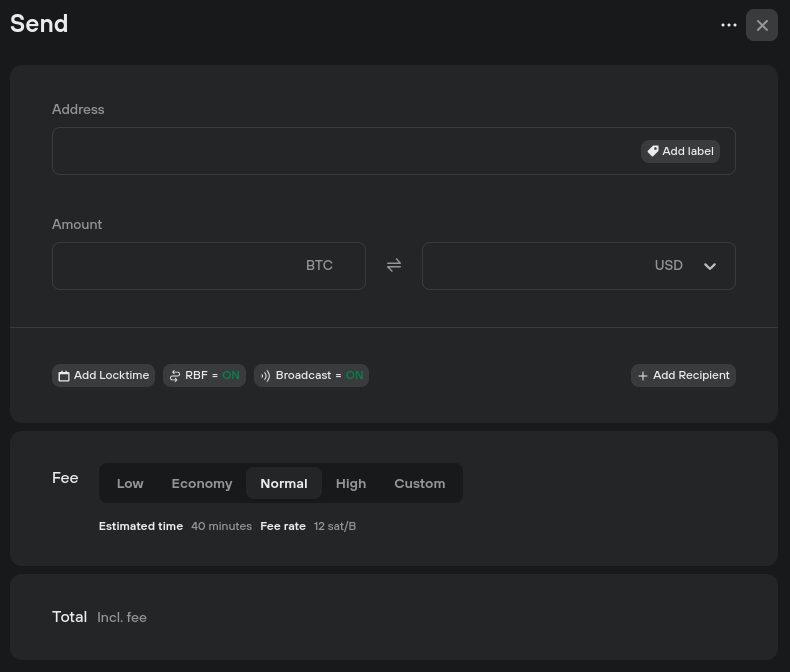
- Confirm transaction details and click ‘Send.’
Check the ‘Overview’ tab if you wish to have a transaction confirmation in your Trezor Suite. You can search for a specific transaction using the ID, label, or amount.
Also, you can export your transaction history in CSV, PDF, or JSON format.
Exchange Crypto in Your Trezor App
Trezor One also features a built-in exchange feature, supported by collaboration with Invity’s exchange providers. This enables wallet owners to trade among cryptos directly from Trezor by using the wallet site.
To perform a trade, you will have to:
- Access the Trezor Wallet site and the account holding the crypto’s that you wish to exchange;
- Click “Trade” and open the exchange tab;
- Enter the number of cryptocurrencies you want to exchange from your wallet. You can specify either the number of coins or the fiat value of those coins;
- Select the assets you wish to receive, and you can select any coin that Trezor supports;
- Set the network fee – you will see four preset values, or you can enter a custom value;
- Click “Compare offers” to see a list of options. Most of which are from crypto exchanges with no KYC requirements;
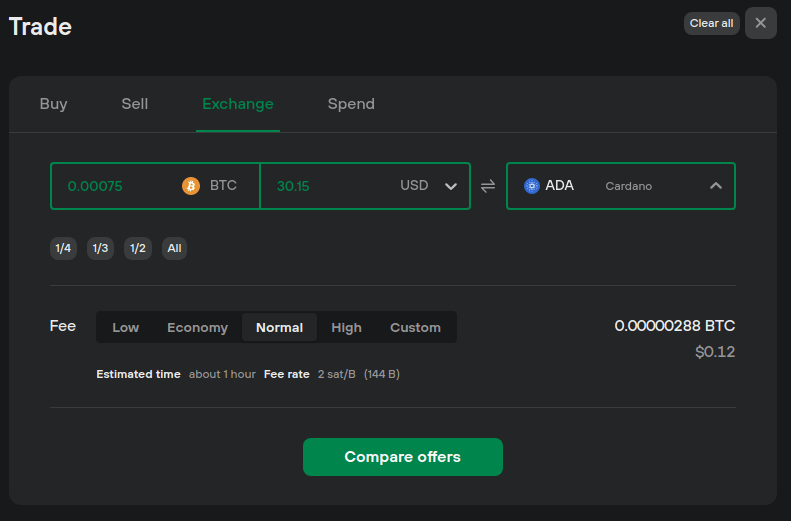
- Determine the offer you would like based on the exchange rate, and click ‘Get this deal’;
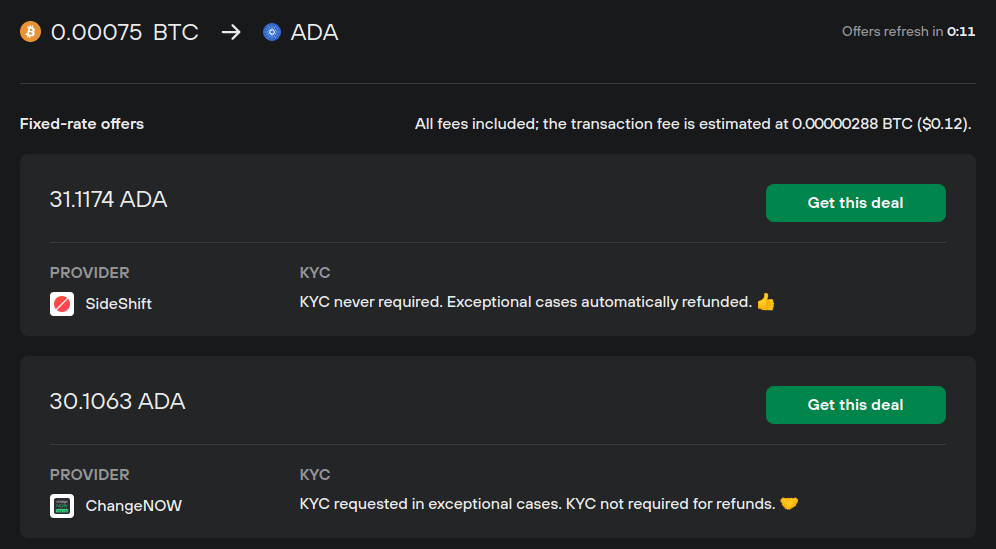
- Last step: agree to the terms and conditions.
Trezor Wallet Fees
The Trezor wallet does not charge any fees when you use the device aside from the money required to buy the actual product and network transaction fees set when making trades.
Trezor Wallet Price
The price of Trezor wallets depends on the model you choose and the website you purchase from. On the official Trezor website, Trezor Model T is sold for $219, and Trezor Model One has a price of $69.
Trezor wallet review: Transaction Times
All crypto transfers and orders are processed within a day; however, the estimated delivery times can vary from one country to another.
Trezor One: Reviewing Security Features
Trezor offers the security features that software wallets can hardly bring. As we have mentioned in any review concerning crypto wallets, security is paramount, and Trezor is a highly secure hardware wallet.
The most important feature of Trezor Model T and Trezor Model One is that they keep funds in cold storage, cutting links to any internet connection.
When set, the device will generate a 24-Word recovery phrase that allows users to restore the wallet in case they lose or break their device.
The seed can also be used on other wallets to recover funds if Trezor ceases to function as a company.
You can also add another word to your recovery phrase to enhance your wallet security. This way, when someone gets a hold of your wallet and recovery phrase, they will not be able to access it without the 25th word.
The device provides high security through a PIN code, which has a clever setup process that combines using the device screen and your computer screen, so your PIN stays hidden.
The wallet does not have pre-installed firmware, allowing you to install the latest version of the interface. It is so secure that it can even be used on computers infected with malware.
Trezor Hardware Wallet: Supported Coins
It is essential to note that while the cold wallet has several supported coins, some known as non-native assets, it can only be managed via third-party wallets like MetaMask.
Trezor One natively supports twelve cryptocurrencies and all ERC20 tokens. For more details about the tokens supported, check out the Trezor coins list.
Trezor Customer Support
Trezor owners can get help with various issues by accessing the site’s FAQs section. The Support Centre also features an active Facebook page where the customer support team delivers quick responses.
Trezor Wallet Reputation
Trezor is regarded as one of the most secure hardware wallets on the market, and the company behind it is revered as a trusted business in the crypto industry.
Trezor Wallet Review: Pros and Cons
Pros:
- Affordable price;
- 100% offline storage;
- Transaction confirmation can only be done through device buttons;
- Compact design;
- Has several coins and tokens supported;
- It can be used even on malware-infected PC.
Cons:
- Not hierarchical deterministic;
- Plastic casing.
Trezor Wallet Verdict
Trezor Model T and Model One are compact wallets that allow users to store and trade their crypto securely in one place.
We hope this review offers you the information you need regarding Trezor wallets. If you need more clarification, check the Trezor vs. Ledger comparison to find more.
The hardware wallets are widely regarded as some of the best in terms of both reputation and affordability. As the oldest hardware wallet available, Trezor is a dependable choice that is highly secure and has a reasonable price.
FAQ
What cryptocurrencies can be stored on Trezor wallets?
Trezor hardware wallets are designed to work with Bitcoin, several widely used cryptocurrencies, and all ERC-20 tokens.
What is the difference between the Trezor Model One and Model T?
The main differentiator is the interface: Trezor Model T is a touch screen device instead of the bright OLED screen of Model One.
Security-wise, Model T can be accessed via PIN & passphrase entry directly on the touchscreen, instead of the Model One, which secures access via computer & mobile. Regardless, both modes are highly secure.
On the backup side, Trezor Model T offers advanced Shamir backup, FIDO2 & U2F authentication standards instead of standard seed backup, and U2F security technology found in Trezor Model One.
What is a seed phrase, and how is it used with the Trezor wallet?
A seed phrase is like a secret code comprising 12, 18, or 24 words that is a backup for most crypto wallets. Whenever you create a new key on your Trezor, the device generates a backup seed phrase to keep your confidential information safe.
So, if anything happens to your Trezor, like if you lose it or it gets damaged, you can use the seed phrase to get your private keys back on a new device. It is like a safety net for your valuable digital assets.
How do I use the Trezor wallet to make transactions?
To make a payment using Trezor Suite, you need to enter the destination address and the amount you want to send. You can also set transaction fees, add labels, and confirm the transactions on your Trezor device for added security.
Once you have approved the transaction, it will be processed, and you will receive a confirmation message. Additionally, there is an option to send raw transactions for advanced users.
What should I do if I lose my Trezor wallet?
If you lose or damage your Trezor device, you should not worry. Trezor is designed with this scenario in mind.
You can restore your funds on a new device if you have your Trezor’s secret recovery phrase (12-, 18-, or 24-word phrase). Enter your recovery phrase into the new device, and your funds will be restored.
Can I use my Trezor wallet on multiple devices?
Yes, you can use Trezor with your Android phone. Trezor is compatible with both Android phones and computers. You can use all wallet features, including crypto purchasing, on both devices.
So, whether you are on the go or at home, Trezor has got you covered through the Trezor Suite app.
How can I contact Trezor customer support?
There are a couple of ways to contact Trezor’s customer support team. You can fill out the website form on their website with your inquiry, and they will get back to you as soon as possible.
Alternatively, you can use the chatbot on their website to speak with a customer support representative in real-time. Both options provide convenient and reliable ways to get help with any issues.
How long does it take to receive a Trezor wallet after ordering?
The standard delivery time for Trezor devices is 3 to 5 business days. This time frame begins once your order is processed and the package has been dispatched. You can track your parcel every step of the way until it arrives at your doorstep, as all packages are fully trackable.
Are there any fees associated with using a Trezor wallet?
Yes, you can set transaction fees in Trezor Suite. When making a transaction, select the desired fee from the available options of Low, Economy, Normal, or High. You can set a custom fee that fits your needs if you still need to.